The shift of business applications and infrastructure to the cloud has increased the need for security teams to comprehensively manage cyber risks, ensuring visibility and control across diverse cloud environments. As organizations increasingly embrace multi-cloud environments, they often find themselves grappling with a fragmented landscape of siled, shortcut-based point solutions. This disjointed approach leaves cloud applications vulnerable to attacks as security costs and complexity mount.
At Qualys, we are deeply committed to innovation that prioritizes our customers' needs and experiences. Our commitment to innovation is not just a strategy; It's a key part of our mission to deliver exceptional value and support to our users every step of the way.
We are excited to share the groundbreaking announcements made at QSC Americas and Mumbai 2024, where we unveiled a series of innovative features that will significantly enhance our customers' cloud security programs. In response to the new challenges facing our customers, we are excited to introduce three powerful new features in Qualys TotalCloud CNAPP that improve threat analysis and context, simplify scalable response, and accelerate time to value for our customers:
Cloud workflow automation for TotalCloud attack path, improved user onboarding and UI
Break presentation chains and visualize context with TotalCloud Attack Path
We are excited to announce the launch of TotalCloud Attack Path. This powerful new feature enhances your cloud security strategy by enabling targeted remediation, breaking chains of exposure, and prioritizing high-impact risks to stop threats in their tracks.
It becomes even more powerful when combined with TruRisk Insights
TruRisk Insights is a game-changing capability in Qualys TotalCloud CNAPP, designed to provide organizations with a unified, prioritized view of their cloud security landscape. By correlating risk indicators from different sources, such as misconfiguration, vulnerabilities, and threats, TruRisk Insights enables security teams to identify the most critical threats and focus on them first instead of getting lost in a sea of data. For example, it can highlight virtual machines with known exploitable vulnerabilities that are also exposed to the Internet, allowing teams to take immediate action. Using TruRisk Insights, organizations can make proactive, data-driven decisions, streamline their threat hunting and risk remediation efforts, and significantly reduce their risk exposure, ensuring they are not only patching vulnerabilities but also effectively eliminating the most pressing threats to their cloud infrastructure. And applications.
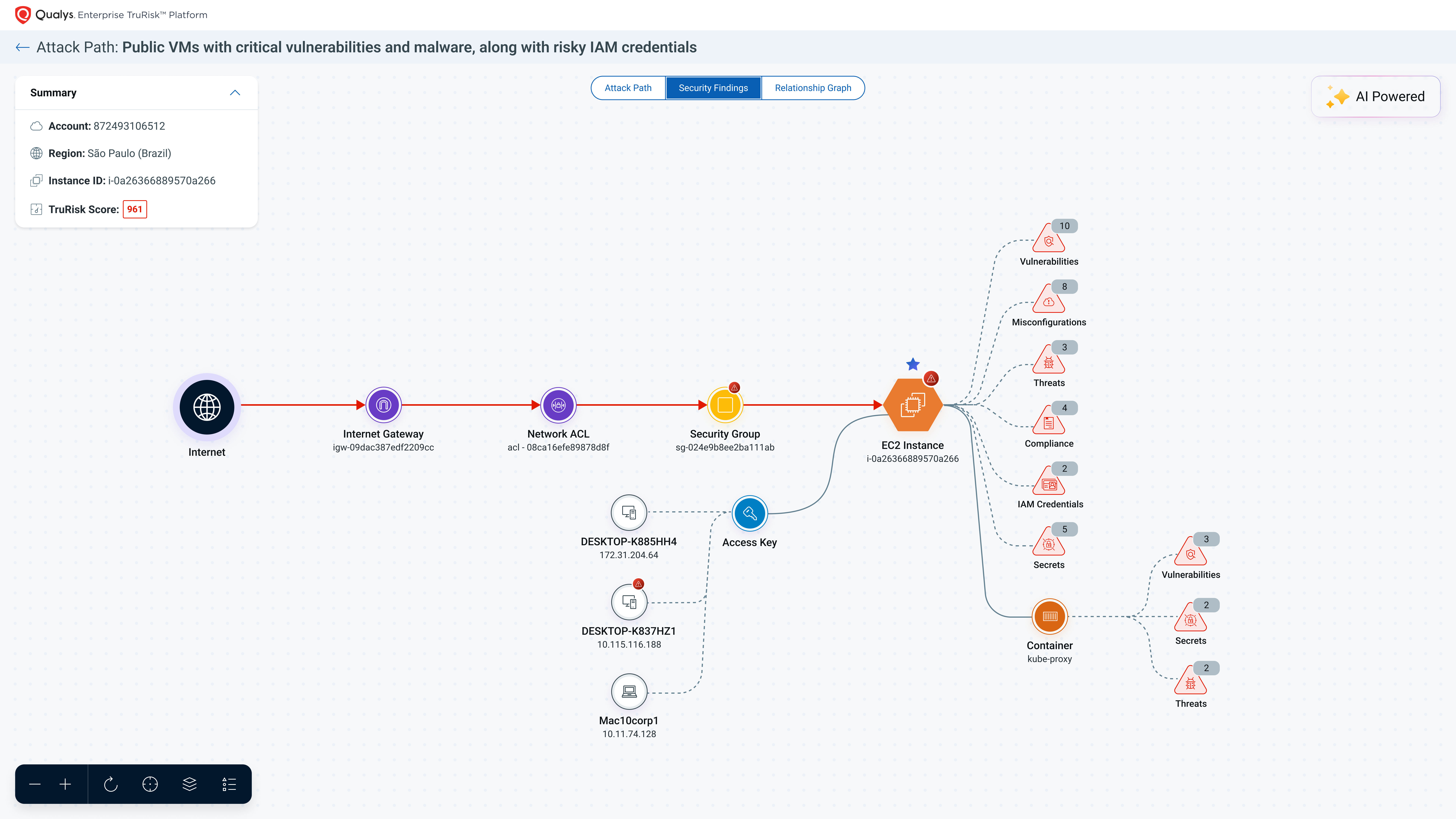
By combining TruRisk Insights with the new TotalCloud Attack Path capability, we significantly enhance security analysts' ability to respond to threats more quickly and effectively. TruRisk Insights provides a comprehensive, prioritized view of risks across your cloud, while Attack Path allows teams to visualize exposure to critical resources, and determine the blast radius of potential vulnerabilities. This combination enables proactive threat analysis, helping analysts identify where they need to focus their efforts. With the ability to prioritize risk outcomes through the security graph, analysts can easily navigate to the most critical resources that require immediate attention. With this new capability, Qualys builds on existing detection and remediation steps by mapping interconnected risks, enabling teams to apply targeted remediation across exposure chains for relevant vulnerabilities. As a result, organizations can scale their response efforts by quickly remediating threats with risk-based priority, ensuring the most urgent vulnerabilities are addressed first. This synergy not only speeds up response times, but also strengthens the overall security posture of the cloud.
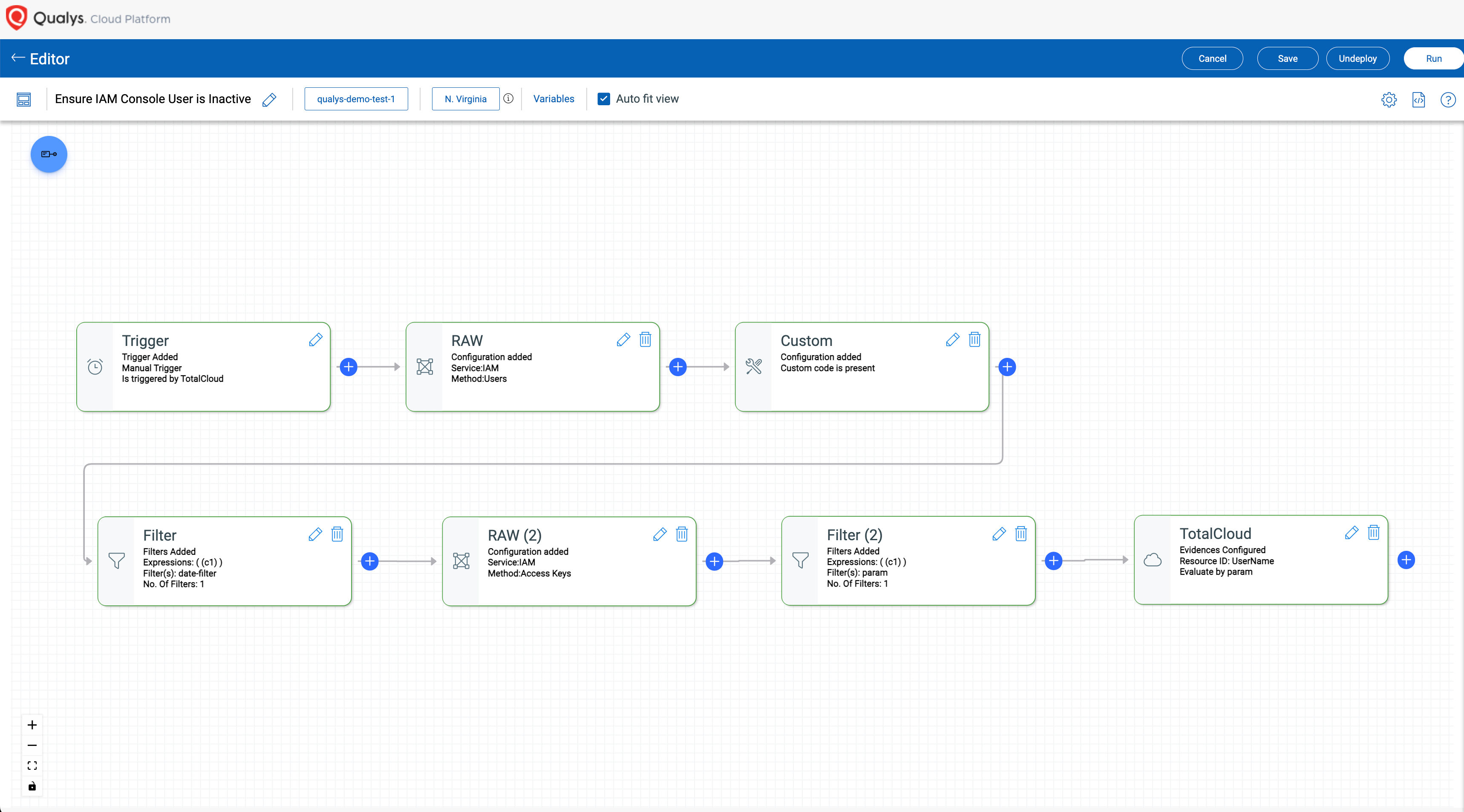
Scale security operations with Cloud Workflow Automation (CWA), enabling last-mile adaptation through personalized detection, continuous data enrichment, personalized analysis, and automated responses – all within a scalable, extensible platform. This intuitive workflow builder allows users to easily create workflows – known as QFlow Playbooks – using a drag-and-drop interface that requires no programming knowledge. With visible nodes representing different functions, security teams can quickly customize workflows to fit their specific needs, whether it's for inventory discovery or coordination of complex remediation tasks. With Cloud Workflow Automation (CWA), teams can adopt and customize workflows within the platform and automate routine security processes with a built-in native solution that boosts efficiency over a set of do-it-yourself (DIY) approaches. The ability to seamlessly integrate with DevOps and ITSM tools further enriches security operations, allowing for a cohesive approach to security program management. Some key capabilities include:
End-to-end orchestration: Automate the entire lifecycle of security operations, from detection to remediation, ensuring a streamlined approach to vulnerability management and compliance across your cloud. Customizable QFlow Guides: Customize workflows to meet specific use cases without programming skills, allowing security teams to quickly adapt to evolving threats and operational requirements. Integration with third-party tools: Seamlessly connect with existing DevOps and IT Service Management (ITSM) tools, helping cross-team collaboration and enhancing overall incident response efficiency. Real-time monitoring and alerts: Set up triggers for instant notifications based on specific events, ensuring security teams can act quickly when potential threats are detected. Reusable workflow guides: Use pre-built playbooks for common security tasks, enabling quick deployment of workflows that can be customized as needed, reducing setup time and effort. Scalability to fit growing environments: Easily scale workflows to accommodate new resources and services as your cloud infrastructure grows, while maintaining consistent security controls across all assets.
Accelerate time to value with an improved UI and user onboarding flow
TotalCloud's 3-step user onboarding UI is designed with ease of use at its core, providing a modern look and feel that simplifies the setup process for integrating their multi-cloud CSP environments. With a simplified three-step onboarding process, users can quickly set up their environment without the steep learning curve often associated with complex security platforms. A guided connector deployment experience guides users through each step, ensuring they understand how to integrate their systems effectively. This value-oriented onboarding flow not only facilitates a smoother transition, but also enables users to take advantage of TotalCloud's capabilities from the start. Within a few minutes of setting up the connectors, users can automatically see a risk and compliance dashboard with their security posture. By focusing on intuitive design and user-friendly navigation, we aim to enhance the overall experience, allowing security teams to get to work and achieve maximum productivity without unnecessary delays. With these improvements, onboarding becomes less of a barrier and more of an opportunity to draw users into TotalCloud's powerful features from day one.
Sign up for a trial of Qualys TotalCloud CNAPP today.
Learn how we can help you on your journey
If you want to dive deeper into CNAPP, download the 2024 Gartner CNAPP Market Guide, explore more about the Qualys TotalCloud platform, get your free customized TotalCloud TruRisk Insights report, read our FAQs, or talk to a Qualys TotalCloud CNAPP expert.