Private Cloud Compute (PCC) meets the computationally intensive demands of Apple Intelligence while providing leading privacy and security protections – by bringing the industry-leading hardware security model to the cloud. In our previous post introducing Private Cloud Compute, we explained that to build public trust in the system, we would take the unusual step of allowing security and privacy researchers to examine and verify PCC's comprehensive security and privacy promises. In the weeks since we announced Apple Intelligence and PCC, we have provided selected third-party auditors and security researchers with early access to the resources we have built to enable this examination, including the PCC Virtual Research Environment (VRE).
Today we are making these resources publicly available to invite all security and privacy researchers – or anyone with a technical interest and curiosity – to learn more about PCC and conduct their own independent verification of our claims. We're excited to announce that we're expanding the Apple Security Bounty program to include PCC, with significant rewards for reporting issues related to our security or privacy claims.
Security guide
To help you understand how we designed the PCC architecture to meet all of our core requirements, we've published the Private Cloud Computing Security Guide. The guide includes comprehensive technical details about the components of PCC and how they work together to provide a leading level of privacy for AI processing in the cloud. The guide covers topics such as: How to build PCCs on a consistent foundation of features implemented in hardware; How to authenticate and route PCC requests to provide non-targeting; How do we technically ensure that you can inspect software running in Apple's data centers; And how the privacy and security features of PCC hold up in different attack scenarios.
Virtual research environment
For the first time ever, we've created a virtual research environment (VRE) for the Apple platform. VRE is a set of tools that enables you to perform your own security analysis of Private Cloud Compute directly from your Mac. This environment allows you to go beyond simply understanding the security features of the platform. You can be sure that Private Cloud Compute actually maintains user privacy with the methods we've described.
VRE runs the PCC node software in a virtual machine with only minor modifications. Userspace works similarly to a PCC node, with the boot and kernel process adapted for virtualization. The VRE includes a Virtual Secure Enclave Processor (SEP), enabling security searching in this component for the first time – and also uses built-in macOS support for near-virtual graphics to enable inference.
You can use VRE tools to:
List and inspect versions of PCC programs Verify transparency log consistency Download binaries corresponding to each version Run the version in a virtual environment Perform inference on demo models Modify and debug the PCC program to enable deeper investigation
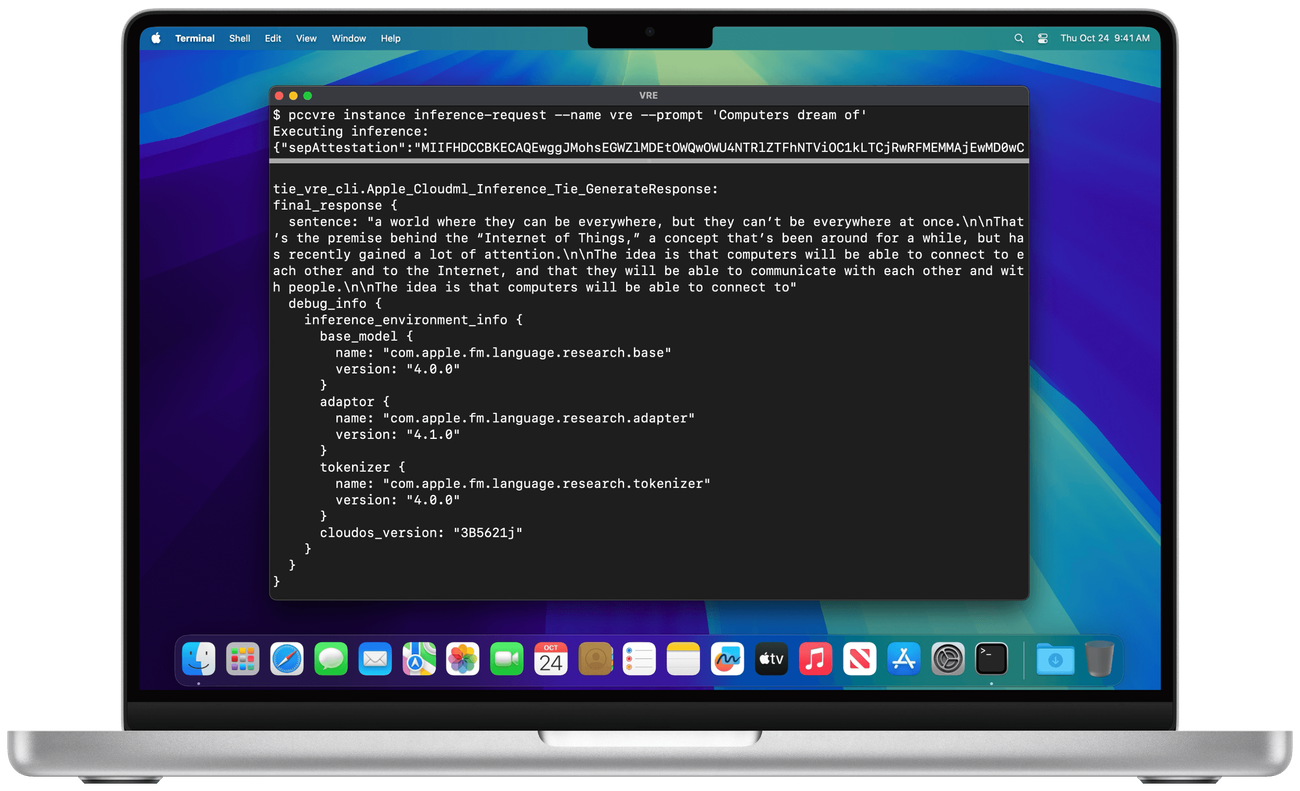
VRE is available in the latest macOS Sequoia 15.1 Developer Preview and requires a Mac with Apple silicon and 16GB or more of unified memory. Learn how to get started in a virtual private cloud computing research environment.
Private cloud computing source code
We also provide the source code for certain key components of PCC that help implement its security and privacy requirements. We provide this resource under a limited-use license agreement to allow you to perform deeper analysis of PCC.
The projects for which we release source code cover a wide range of PCC areas, including:
CloudAttestation project, responsible for generating and validating PCC node certificates. The Thimble project, which includes the Privatecloudcomputed daemon running on a user's machine and uses CloudAttestation to enforce verifiable transparency. The splunkloggingd daemon, which filters logs that could be emitted from the PCC node to protect against inadvertent data disclosure. The srd_tools project, which contains the VRE tools and which you can use to understand how to enable the VRE to run PCC code.
You can find the PCC source code available in the apple/security-pcc project on GitHub.
Apple Security Bonus for Private Cloud Computing
To further encourage your research into private cloud computing, we're expanding the Apple Security Bounty program to include bounties for vulnerabilities that demonstrate compromise of PCC's core security and privacy safeguards.
Our new PCC reward categories align with the most significant threats we describe in our Security Guide:
Accidental data disclosure: Vulnerabilities that lead to inadvertent data disclosure due to configuration flaws or system design issues. External compromise of user requests: Vulnerabilities that enable third parties to exploit user requests to gain unauthorized access to PCC. Physical or internal access: Weaknesses where access to internal interfaces allows the system to be compromised.
Because PCC extends the industry-leading security and privacy of Apple devices to the cloud, the rewards we offer are comparable to those of iOS. We award maximum amounts for vulnerabilities that compromise user data and infer request data outside PCC's bounds of trust.
Apple Security Bonus: Private Cloud Computing
Category Description Maximum Reward Remote attack on request data Execution of arbitrary code with arbitrary entitlements $1,000,000 Access to user request data or sensitive information about user requests outside of trust boundaries $250,000 Attack on request data from a privileged network location Access to user request data or Other Sensitive user information outside the bounds of trust USD 150,000 Ability to execute undocumented code USD 100,000 Accidental or unexpected data disclosure due to a deployment or configuration issue USD 50,000
Because we care deeply about any user privacy or security compromise, we will consider any security issue that has a significant impact on PCC for the Apple Security Bounty, even if it does not match a published category. We'll evaluate each report based on the quality of what is delivered, the evidence of what can be exploited, and the impact it has on users. Visit our Apple Security Bounty page to learn more about the program and to submit your research.
in conclusion
We designed Private Cloud Compute as part of Apple Intelligence to take an extraordinary step forward for privacy in AI. This includes providing verifiable transparency – a unique property that sets it apart from other server-based AI approaches. Building on our experience with the Apple Security Research Device Program, the tools and documentation we released today make it easier than ever for anyone to not only study, but verify important security and privacy features of PCC. We hope you'll delve deeper into the design of PCC through our security guide, explore the code yourself through the virtual research environment, and report any issues you find through the Apple Security Bounty. We believe private cloud computing is the most advanced security architecture ever deployed for intelligent cloud computing at scale, and we look forward to working with the research community to build trust in the system and make it more secure and private over time.



