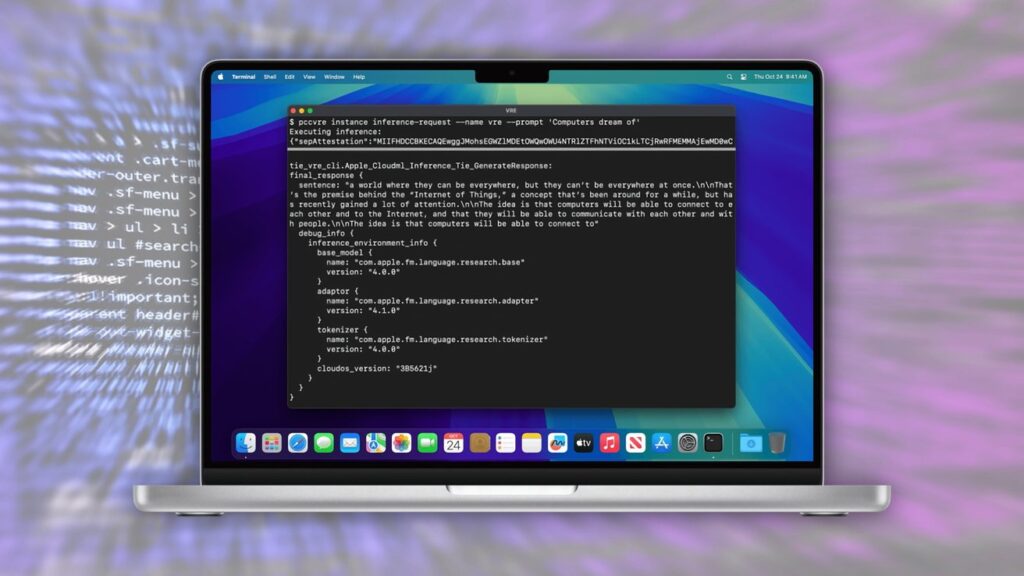
Virtual environment for testing private cloud computing – Image credit: Apple
Apple advised at launch that Private Cloud Compute's security would be inspectable by third parties. On Thursday, she fulfilled her promise.
In July, Apple introduced Apple Intelligence and its cloud processing facility, Private Cloud Compute. It was presented as a secure and private way to handle cloud processing of Siri queries within Apple Intelligence.
In addition to insisting that it uses encryption and does not store user data, it also insists that features can be vetted by independent experts. On October 24, it offered an update on that plan.
In a post on the Security Research blog titled “Security Research into Private Cloud Computing,” Apple explained that it has provided third-party auditors and some security researchers with early access. This included access to resources created for the project, including the PCC Virtual Research Environment (VRE).
The post also says the same resources became available to the public as of Thursday. Apple says this allows all security and privacy researchers, “or anyone with a technical interest and curiosity,” to learn about how Private Cloud Compute works and conduct their own independent verification.
resources
The release includes a new guide to private cloud computing security, which explains how to design the architecture to meet Apple's core requirements for the enterprise. It includes technical details of the components of PCC and how they work, how authentication and request routing occur, and how security withstands different forms of attack.
The VRE is Apple's first ever for any of its platforms. It consists of tools to run PCC node software on a virtual machine.
This is not specifically the same code used on the servers, as there are “minor modifications” needed to make it work locally. Apple insists that the software works identically to the PCC node, with only changes made to the boot process and kernel.
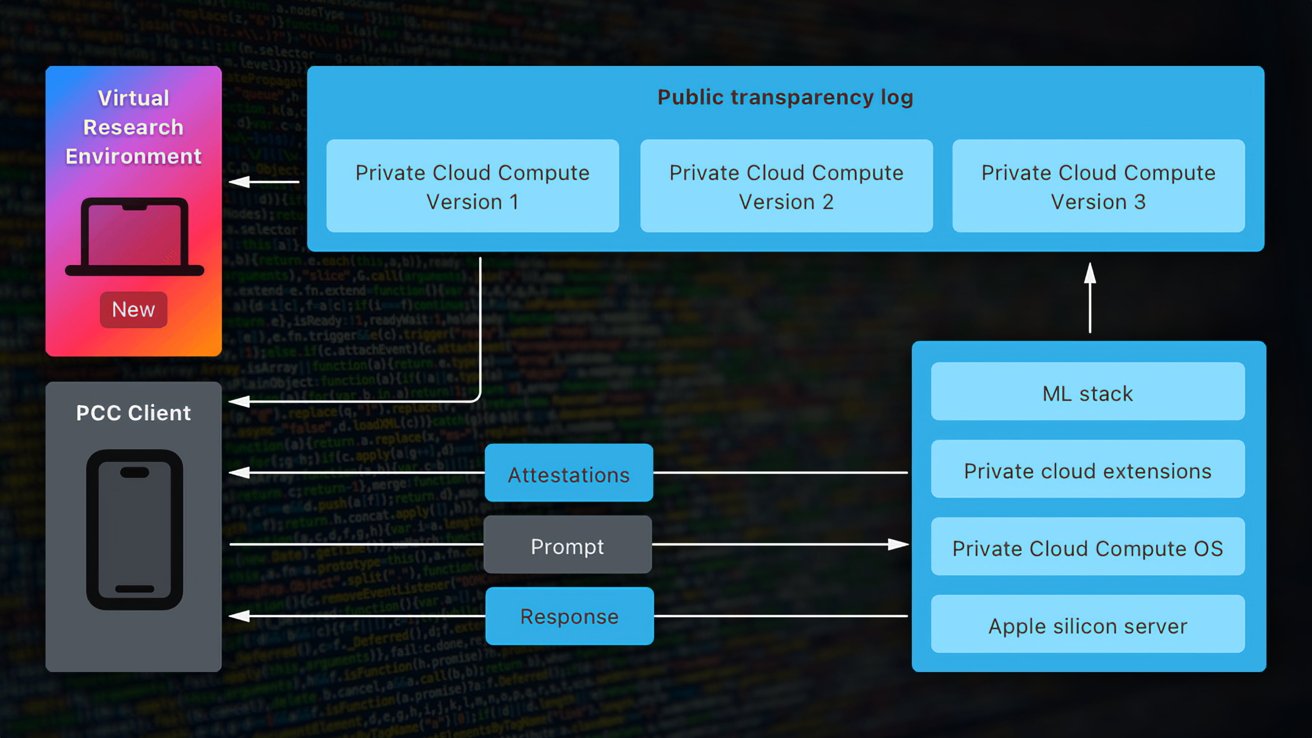
A diagram showing how private cloud computing elements interact with the new virtual research environment – Image credit: Apple
VRE also includes a virtual Secure Enclave processor, and takes advantage of macOS' built-in support for near-virtual graphics.
Apple is also making the source code for some key components available for inspection. The source code is provided under a limited-use license intended for analysis, and includes the CloudAttestation project to generate and validate PCC node certificates.
There's also the Thimble project, which includes a daemon for the user's device that works with CloudAttestation to verify transparency.
PCC bug bounty
Furthermore, Apple is expanding the range of Apple Security Bounty rewards. It promises “big rewards” for reporting security and privacy issues with Private Cloud Compute.
The new categories in the bounty correspond directly to the critical threats listed in the Security Guide. This includes inadvertent data disclosure, external hacking of user requests, and physical or internal access vulnerabilities.
The award range starts at $50,000 for accidental or unexpected disclosure of data due to a deployment or configuration issue. At the top of the scale is the ability to prove arbitrary code execution with arbitrary entitlements, which can earn participants up to $1 million.
Apple adds that it will consider any security issue that has a “significant impact” on the PCC for a potential award, even if it doesn't fit into one of the specified categories.
“We hope you will delve deeper into the design of PCC through our security guide, explore the code yourself using the virtual research environment, and report any issues you find through the Apple Security Bounty,” the post said.
In conclusion, Apple says it designed PCC to “take an extraordinary step forward for privacy in AI,” including verifiable transparency.
“We believe private cloud computing is the most advanced security architecture ever deployed for intelligent cloud computing at scale, and we look forward to working with the research community to build trust in the system and make it more secure and private over time,” the post concludes.